Prof. K. Subrahmanian of IEEE delivers a Guest Lecture on Cyber Security
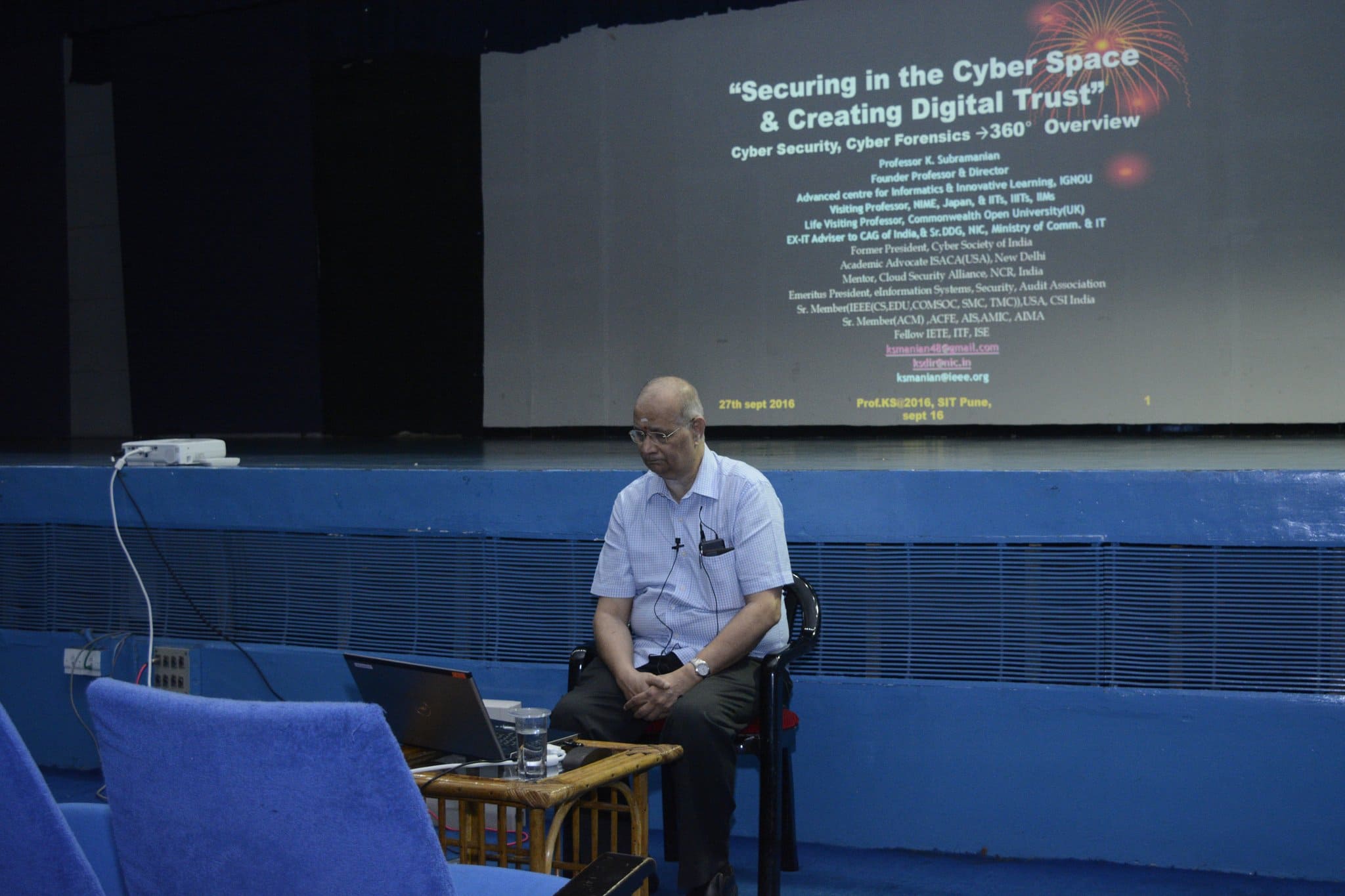
Cyber Security , Cyber Frauds, Cyber Forensics : An Overview
On 27th September 2016 we had a special guest; The vice Chair of the IEEE Prof. K. Subramanian. His session on started with an introduction on the topic “Cyber Security, Cyber Frauds & Cyber Forensics” by Prof K. Subramanian. He is the Vice Chair of IEEE Delhi Section, Vice Chair of IEEE Education Society, IEEE EMS, IEEE CS (Delhi Section). He is also the Mentorcum Adviser CSA, NCT Delhi. He is the founder Director & Professor, Advanced center for Informatics & Innovative Learning, IGNOU & EX- SR. DDG(NIC), Min of C & IT & IT Adviser to CAG of India
Academic advocate, ISACA, New Delhi.
The agenda of the lecture was to introduce the students with the topic and its relevance in today’s world. The lecture included the past and present security trends, security perspective for the converged networks, security optimization & layered defense, multi media security and the cyber forensics.
Prof Subramanian threw some light on the typical cyber scenario which is dynamic, undefined and exponential. It is a virtual space where netizens exist, citizens don’t. The present society lacks the IT maturity and there is an absence of a single governing authority. Management does not worry about a cyber attack until and unless it results in an financial, customer, reputation or credibility loss. In the Era of Digital Age there are some important imperatives such as IT & Law, Security & Risk, Governance funding, Alignment & Collaboration and many more.
Mr. Subramanian rightly pointed out the difference between the Security of assumptions in 1998 and 2016. In 1998 when internet was considered to be the enemy, virus protection to be the key, password protection a priority, ad-hoc intrusion detection was considered sufficient. But the scenario has changed today. Now attacks are primarily generated from the victims with no intent. Ad-hoc intrusion detection is not sufficient, virus protection is less reliable and deep packet inspection (layer 2-7) is mandatory.
He briefly described many of the software technologies for risk mitigation such as encryption technology, steganography, digital watermarking, ILM technologies and many more. Also introduced the students with Computer and Digital Forensics and their need in present era. Cyber Forensics has become a new challenge now due to evidence, environment and identity management.
As the world becomes more connected and our vulnerability increases, the need for more comprehensive security will become imperative for everyone from small businesses to multinational corporations—and, of course, for their customers. The opportunity is staggering.